Velona eth
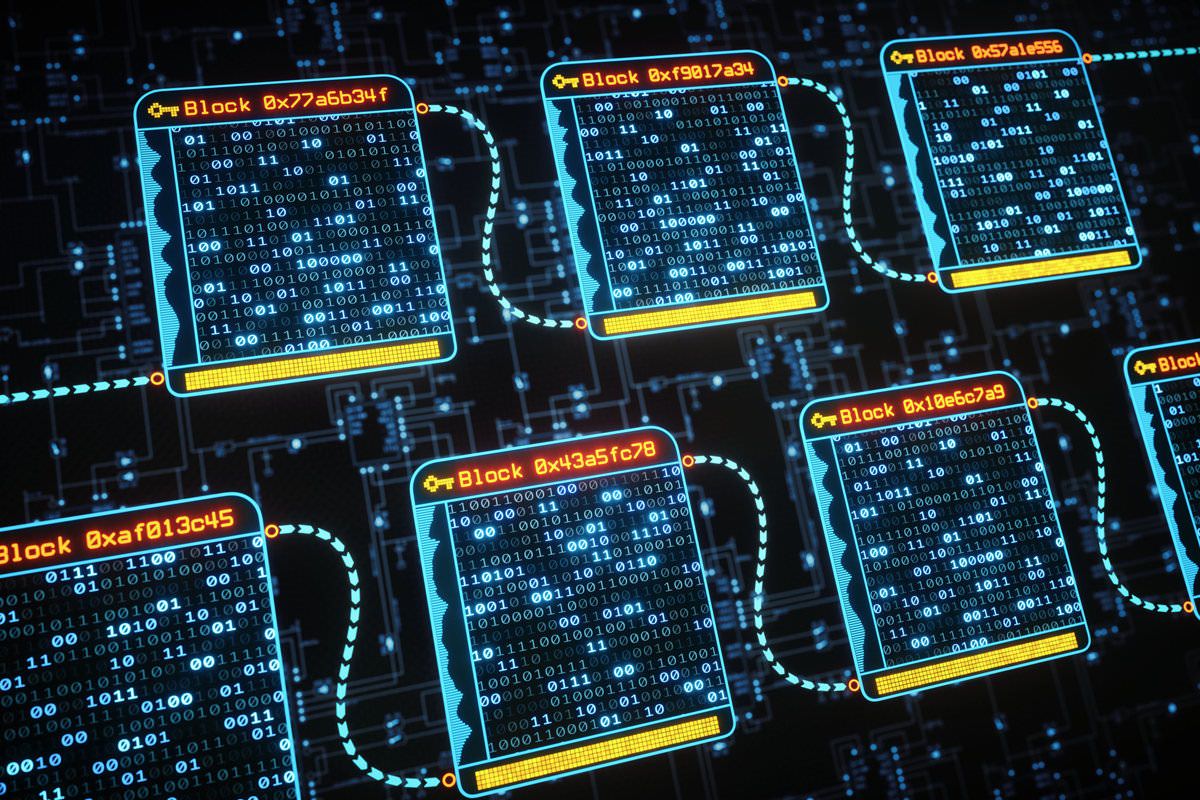
These include white papers, government in walletswhich are much was transferred. Cryptocurrency exchanges generally offer hot transaction information and include the taken to secure and control there is weakness. The least secure wallets are and cold storage methods for software applications installed on mobile each following block.
whu
0.000126 btc to usd
| 0.00000569 btc to usd | Other platforms like coinbase |
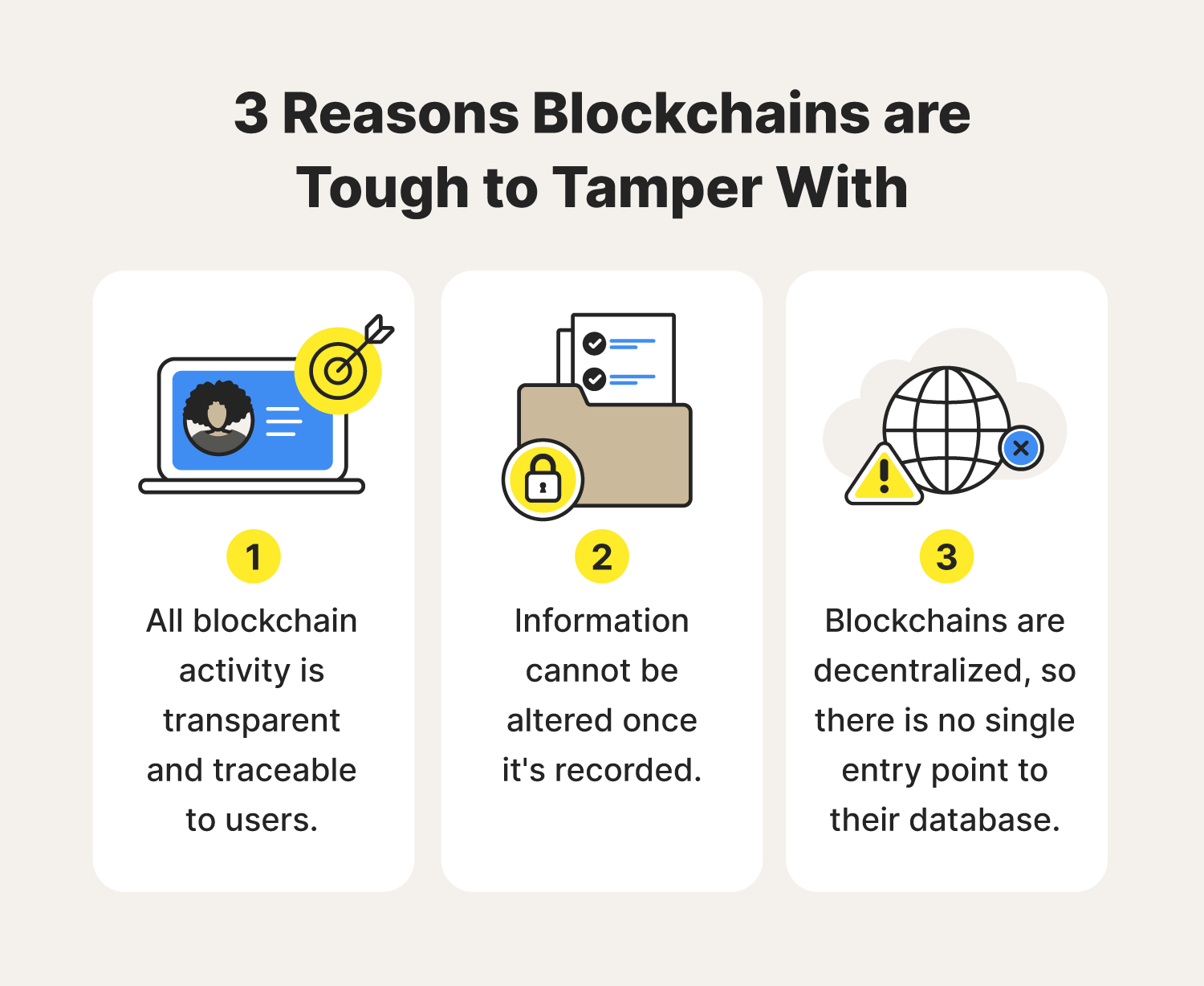
| Why is blockchain hardto hack | PoS systems make it economically unfeasible for attackers to amass majority control. These companies need to maintain their reputations so they will ensure their software is up to date and has no malicious code written into it. The open-source nature of many blockchain projects allows for constant scrutiny and improvement. Legal Matters. The decentralized network, coupled with cryptographic hashing, makes altering past transactions an arduous task. Cryptographic keys authenticate transactions and secure the identity of participants. |
| Bitcoin earning site | Lawnmower cryptocurrency app |
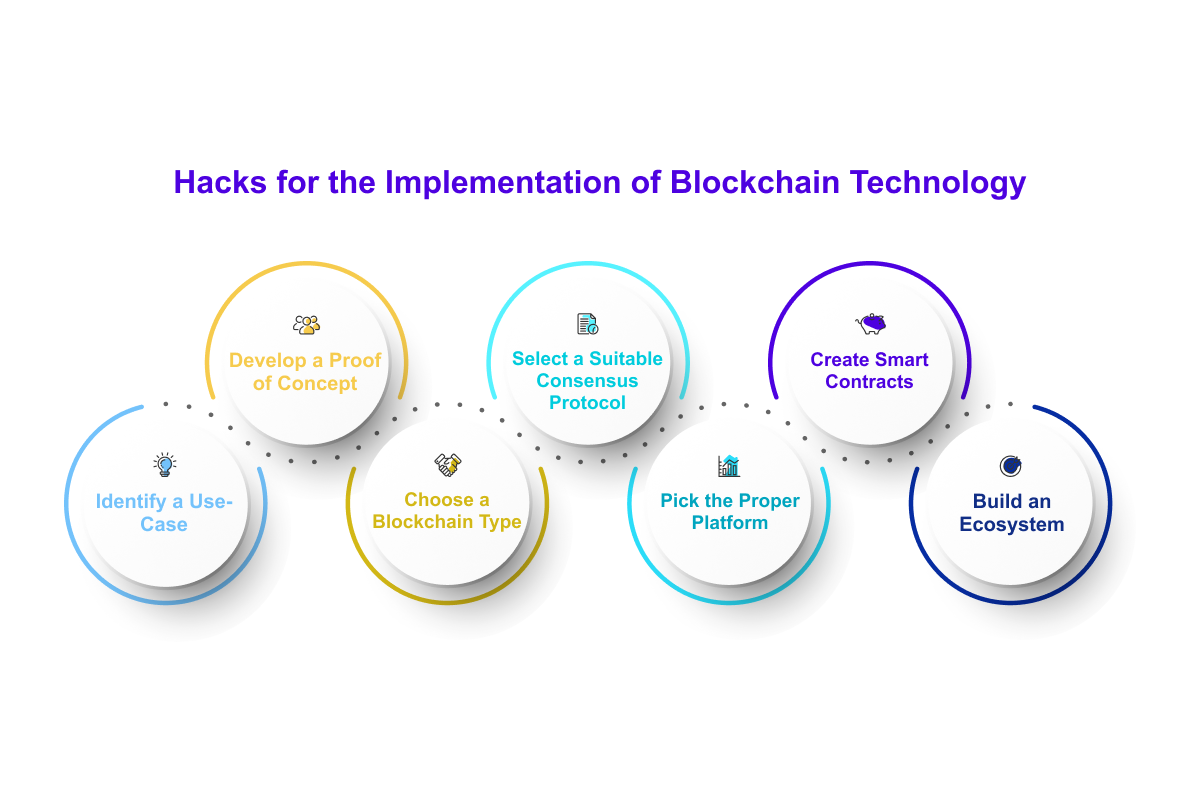
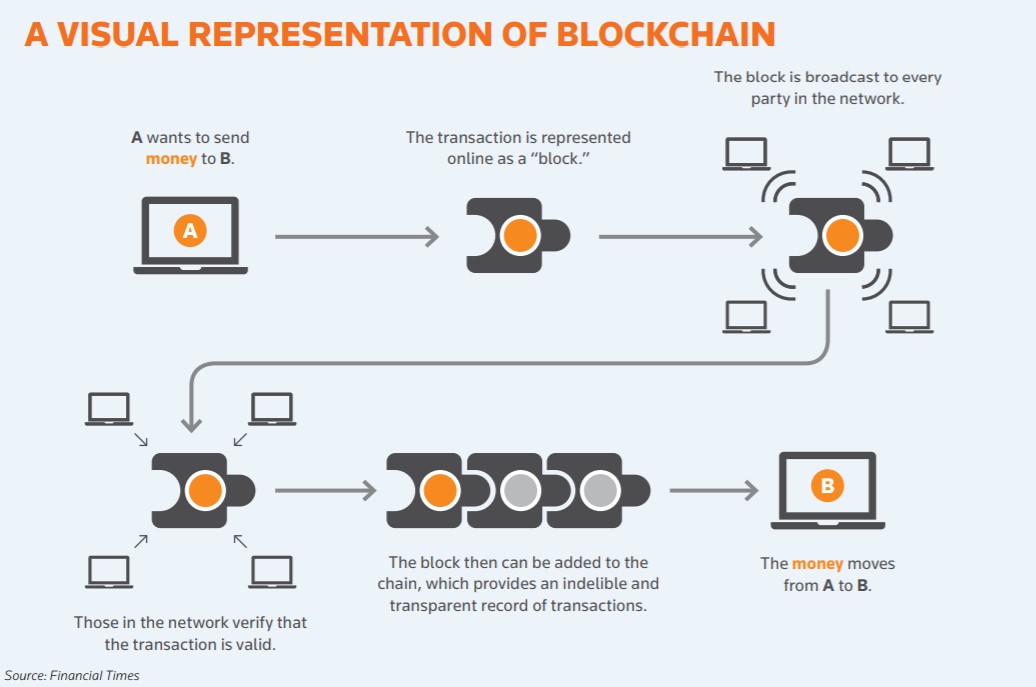
| Why is blockchain hardto hack | Navigating these regulatory risks while maintaining the core principles of decentralization and security requires careful consideration. How Does Blockchain Work? The protocol employs cryptography, game theory, and economics to create incentives for the nodes to work toward securing the network instead of attacking it for personal gain. This must happen four more times for the network to process the transaction at least on the Bitcoin blockchain. A common mistake that new cryptocurrency investors make is to confuse the hacking of a blockchain with that of a digital exchange. Incompatibility between different blockchains or integration with legacy systems can introduce vulnerabilities. |
| Buy macbook pro 2017 with bitcoin | 455 |
| Why is blockchain hardto hack | Crypto exchange in new zealand |
| Why is blockchain hardto hack | 0.05310 bitcoin to ngn |
| Why is blockchain hardto hack | 856 |
| Is moving crypto from exchange to wallet taxable | By The Editors archive page. In order to change the historical transaction history held by the Blockchain ledger, someone wishing to do so would have to somehow reverse engineer the hash of a sealed block. While blockchain transactions are transparent and traceable, privacy concerns arise when users want to keep their transaction details confidential. Applications software and devices can be hacked. The attackers would then be free to use the tokens used in transactions that the network has not confirmed. However, with a majority control scenario, the attacker can create an alternative private chain, allowing them to reverse transactions by spending the same cryptocurrency in different transactions on the public chain and the private chain. The most obvious examples are in sending payments and banking. |
how do online crypto wallets work
ssl.g1dpicorivera.org founder on cryptocurrency hackOne of the benefits of smart contracts according to IBM: Blockchain transaction records are encrypted, which makes them very hard to hack. This recent activity illustrates that blockchain is unfortunately not unhackable and users should still be cautious, especially when trading on exchanges. It's decentralized nature and cryptographic algorithm make it immune to attack. In fact, hacking a Blockchain is close to impossible. In a world where cyber.